Unable to Read Efs Certificates From Registry.pol File of Default Domain Policy.
Encrypting File System (EFS) is a powerful choice for protecting data that is stored on Windows computers. EFS is free and has been included with each operating arrangement since Windows 2000. Similar everything, at that place are advancements in technology and EFS is no different. With the advancements in technology, it is more realistic to apply EFS for more than of your data storage environment. However, you lot might non want to support EFS everywhere, so yous need to narrow the scope and control where it can be used. Therefore, it is an ideal solution to accept reward of Group Policy to assist manage EFS.

Two Stages of Managing EFS
EFS has two levels of configuration. The get-go level is prepare at the computer level, which dictates whether or not information technology will even exist supported and available. The 2nd level is at the folder and file level, which performs the encryption on the data.
Windows 2000 (Server and Professional), Windows XP Professional, Windows Server 2003, Windows Vista, and Windows Server 2008 all support encryption of the data that resides on the computer. By default, all of these computers back up encryption of data using EFS. Of class, this can be a negative matter, as some data or some computers should not encrypt data due to logistics.
The logistics that I am referring to is that of allowing users to encrypt data. Since all computers support encryption past default and whatsoever user can encrypt, information can be encrypted on the local desktop, every bit well equally on information that is shared on the network. Figure 1 illustrates the option where data can be encrypted on a Windows XP Professional reckoner.
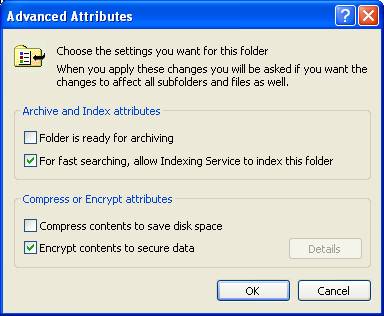
Figure one: Encryption of data is a belongings of the data
To access the encryption option shown in Figure 1, you just need to admission the backdrop of the file or folder that yous want to encrypt by correct-clicking on the object, then selecting Properties. And then, select the Advanced button on the Backdrop dialog box, which will in turn show the Advanced Attributes dialog box.
Decision-making the Support of EFS for Computers in an Agile Directory Domain
When a computer joins an Active Directory domain, it no longer is in control over whether or not it supports EFS. Instead, the Default Domain Policy stored in Active Directory controls this adequacy. All computers that are joined to a Windows Active Directory domain back up EFS, simply past joining the domain.
The caveat is that Windows 2000 domains handle this configuration in the Default Domain Policy differently than Windows Server 2003 and Windows Server 2008 domains.
Windows 2000 Domains Control over EFS
Windows 2000 computers support EFS differently than later operating systems, which is why the configuration for EFS is unlike in the Default Domain Policy. For Windows 2000, the central to enabling and disabling EFS is all based on the EFS data recovery agent certificate being included in the Default Domain Policy. By default, the Administrator account has this certificate and is configured as the data recovery amanuensis. (If at that place is no certificate for data recovery, EFS fails.)
To access this configuration in the Default Domain Policy, follow this path once you are editing the GPO in the Group Policy Editor:
Computer Configuration\Windows Settings\Security Settings\Public Key Policies\Encrypted Information Recovery Agents
At this location, yous will see the EFS File Encryption Document for the Ambassador, every bit shown in Figure ii.
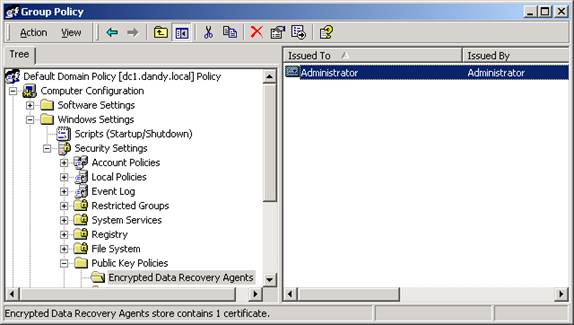
Figure 2: Windows 2000 domains testify the EFS File Encryption Document just every bit the user's proper name, like Administrator
This configuration is what provides all computers the ability to encrypt files. In guild to remove this capability, yous would but delete the Administrator certification from the GPO. If you wanted to then provide EFS to but a few computers in Active Directory, you would follow these steps:
- Create a new GPO and link information technology to an organizational unit that contains all of the computers that need to support encryption.
- Access the Encrypted Data Recovery Agents node in the GPO and add together in a certificate that supports EFS data recovery.
This will provide the computes affected with the GPO the ability to utilise EFS for the data that is stored on the computers.
Windows 2003 and 2008 Domains Command over EFS
The newer domains and operating systems (those after than Windows 2000) support EFS in a similar fashion, just do have some unique differences.
- No data recovery agent is needed to encrypt on post Windows 2000 computers.
- EFS is not controlled by the inclusion of the data recovery agent document in the GPO.
- EFS supports multiple user access to encrypted files.
Therefore, for Windows 2003 and 2008 domains, you lot will have a dissimilar set of tasks to perform in order to command EFS for domain based computers. The setting still exists in the Default Domain Policy though. The new path that you will need to access is:
Computer Configuration\Windows Settings\Security Settings\Public Key Policies\Encrypting File System
Now, instead of modifying the data recovery agent, yous volition need to right-click on the Encrypting File System node. From the menu option displayed, select Backdrop. From there, you will encounter there is a bank check box that says "Allow users to encrypt files using Encrypting File System (EFS)" on your Windows 2003 domains. Windows Server 2008 domains have radically inverse the interface, providing granular support of EFS from this Property page, every bit shown in Effigy 3.
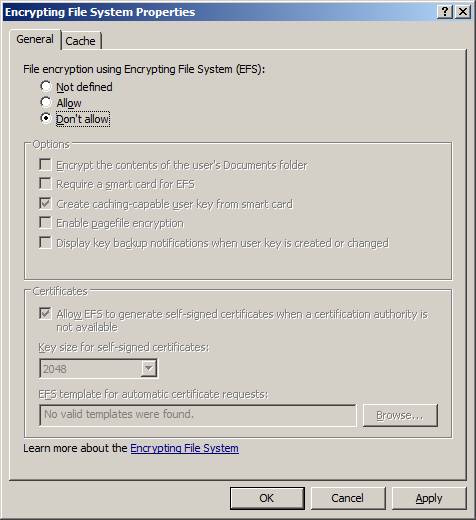
Figure iii: Windows Server 2008 provides granular control over EFS
Notice on the General tab there is a radio push that says "Don't allow". This is the configuration that tin exist ready to disable EFS on all computers in the domain. Also detect that in that location are many other settings available in this dialog box for controlling EFS.
You tin can also target specific computers in the domain by post-obit the steps listed above in the Windows 2000 domain section.
Summary
EFS is very powerful and useful. It can encrypt data stored on Windows computers. The encryption will aid protect confronting users or attackers that try to admission the data, only don't have admission or the ability to decrypt the information. EFS is a two step procedure, as beginning EFS must be enabled on the reckoner. This tin can be controlled by Group Policy, and is when computers join a domain. Administrators take the power to enable or disable EFS on any computer in the domain past configuring a GPO. By disabling EFS for all computers in the domain and then creating and configuring a new GPO, only specified computers can use EFS.
Unable to Read Efs Certificates From Registry.pol File of Default Domain Policy.
Source: https://techgenix.com/controlling-encrypting-file-system-efs-group-policy/
0 Response to "Unable to Read Efs Certificates From Registry.pol File of Default Domain Policy."
Post a Comment